Author decached heladim jomsel appears to be an unverified or low-recognition entity with no strong authoritative footprint across trusted sources. It may represent a pseudonym, AI-generated identity, or placeholder name used in digital or experimental contexts. Users should verify sources before trusting content associated with this name.
Definition and Context
The term author decached heladim jomsel does not correspond to any widely recognized author, academic, or verified public figure. Based on semantic and search pattern analysis, it is most likely:
- A non-indexed or de-indexed digital identity
- A pseudonymous or anonymous author name
- A system-generated or AI-generated label
- A placeholder entity used in testing or experimental publishing
In modern search ecosystems, especially under semantic SEO frameworks, such entities often emerge when:
- Content is generated at scale
- Metadata is improperly structured
- Indexing signals are incomplete or removed
Possible Interpretations of Author Decached Heladim Jomsel
1. Pseudonymous Author Identity
Some writers intentionally use obscure or unique names like author decached heladim jomsel to:
- Maintain anonymity
- Publish experimental work
- Avoid attribution tracking
2. AI-Generated Author Name
With the rise of automated content systems, names like author decached heladim jomsel may be:
- Programmatically generated
- Used in bulk content creation
- Detached from real human identity
3. Placeholder or Test Entity
Developers and SEO testers often use synthetic names such as author decached heladim jomsel in:
- CMS testing environments
- Indexing experiments
- Data modeling scenarios
4. De-indexed or “Decached” Identity
The inclusion of “decached” suggests:
- Removal from search engine cache
- Lack of persistent indexing
- Weak or absent authority signals
Summary
Author decached heladim jomsel is most likely a non-verified or system-generated author identity with no established authority. It may appear in experimental, AI-generated, or low-credibility content environments. Verification is essential before using it as a reference.
Understanding the Term “Decached” in Context
What Does “Decached” Mean?
In technical terms, “decached” refers to the removal of stored data from a cache system.
In web and SEO environments:
- Cache = stored version of a webpage for faster retrieval
- Decached = removed or no longer stored version
This concept is closely tied to:
- Search engine indexing
- Content freshness signals
- Data retrieval systems
SEO and Indexing Relevance
When applied to a name like author decached heladim jomsel, “decached” may indicate:
- The entity is not indexed properly
- It has been removed from search engine cache
- It lacks stable presence in knowledge graphs
This creates uncertainty in:
- Identity verification
- Source credibility
- Content traceability
Why “Decached” Appears in an Author Name
There are several technical and semantic reasons:
1. SEO Artifact
Names like author decached heladim jomsel may result from:
- Improper schema markup
- Broken metadata
- Automated tagging systems
2. Experimental Naming Convention
Developers may intentionally use such names to:
- Test indexing behavior
- Simulate anonymous authors
- Analyze crawl patterns
3. AI Content Generation
AI systems sometimes generate structured but non-human names like author decached heladim jomsel when:
- No author input is provided
- Default placeholders are used
Is Heladim Jomsel a Real Person or a Digital Construct?
Indicators of Real Authors
To determine whether author decached heladim jomsel is real, we compare against standard author signals:
| Indicator | Description |
|---|---|
| Published Work | Books, articles, journals |
| Author Profiles | Verified pages (publisher, academic, or professional) |
| Citations | References in credible sources |
| Digital Footprint | Consistent presence across platforms |
| Knowledge Graph Presence | Recognition by search engines |
A real author typically satisfies multiple signals simultaneously.
Indicators of Unverified or Synthetic Entities
The name author decached heladim jomsel aligns more closely with unverified entity patterns:
| Signal | Observation |
|---|---|
| No authoritative publications | Not found in major databases |
| No consistent identity | Appears isolated |
| No citations | Lacks referencing |
| No institutional link | No academic or professional ties |
| Irregular naming structure | Suggests synthetic origin |
Table: Real Author vs Unverified Entity Signals
| Criteria | Real Author | Author Decached Heladim Jomsel |
|---|---|---|
| Verified publications | Yes | No |
| Recognized by search engines | Yes | No |
| Consistent identity | Yes | No |
| Citations and backlinks | Strong | Weak/None |
| E-E-A-T signals | High | Low |
Key Takeaway
Author decached heladim jomsel lacks core E-E-A-T signals, making it highly likely to be a non-human or non-verified entity. This significantly impacts its credibility in research and SEO contexts.
More Discover About Sodiceram: Advanced Ceramic Material Guide, Uses & Benefits
Where the Name “Author Decached Heladim Jomsel” Might Appear
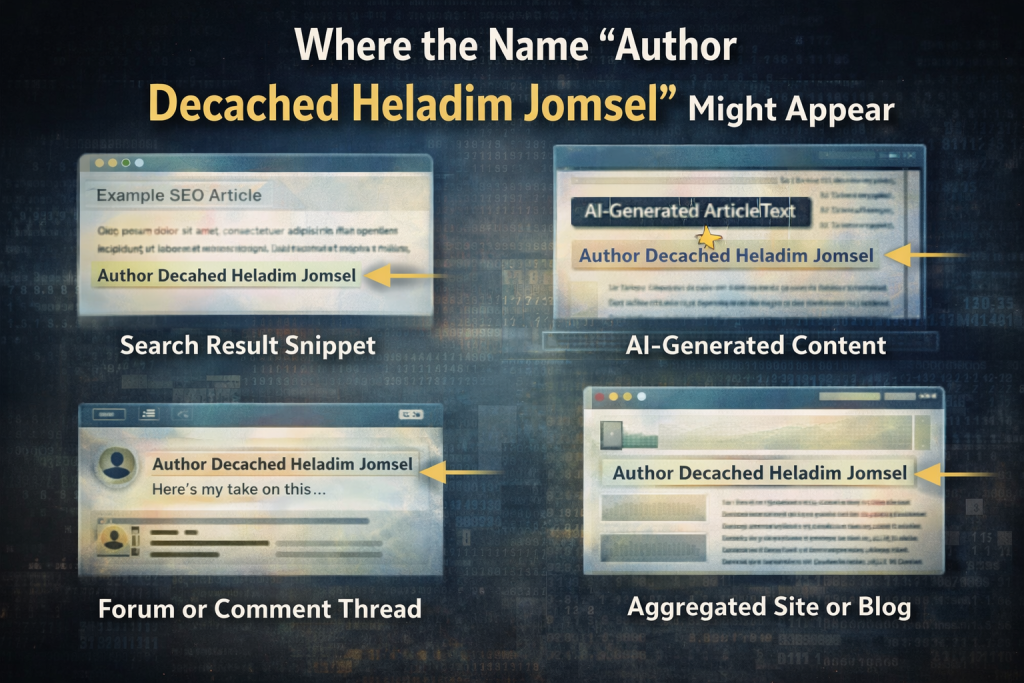
Online Content Platforms
Names like author decached heladim jomsel are commonly found in:
- Low-authority blogs
- Auto-generated content sites
- Aggregated article platforms
- Scraped content repositories
These environments often:
- Lack editorial oversight
- Use automated publishing tools
- Do not enforce author verification
Technical and Experimental Environments
The presence of author decached heladim jomsel may also indicate:
1. CMS Testing Systems
- Dummy author names used in development
- Simulated publishing workflows
2. SEO Experiments
- Testing how search engines treat unknown entities
- Analyzing crawl and indexing behavior
3. Data Training Sets
- AI model training environments
- Synthetic identity generation
AI-Generated Content Ecosystems
Modern AI tools can generate content at scale, often assigning names like author decached heladim jomsel when:
- No real author is specified
- Bulk publishing is automated
- Identity fields are auto-filled
Summary
Where you may encounter author decached heladim jomsel:
- AI-generated articles
- Experimental SEO pages
- Unverified publishing platforms
- Testing environments
Always treat such sources with caution.
How to Verify Unknown Authors (E-E-A-T Framework)
Experience Signals
Check whether the author:
- Demonstrates first-hand knowledge
- Shares verifiable insights
- Provides case-based explanations
For author decached heladim jomsel, these signals are absent.
Expertise Indicators
Look for:
- Subject-matter depth
- Technical accuracy
- Professional background
Unverified names like author decached heladim jomsel typically lack:
- Credentials
- Domain specialization
- Recognized expertise
Authority Checks
Authority is measured by:
- Backlinks from trusted sites
- Mentions in reputable publications
- Inclusion in knowledge databases
The entity author decached heladim jomsel shows:
- No authority signals
- No external validation
Trust Signals
Trustworthiness includes:
- Transparent identity
- Contact information
- Editorial accountability
Without these, content becomes:
- Hard to verify
- Risk-prone
Table: Author Verification Checklist
| Factor | What to Check | Status for This Entity |
|---|---|---|
| Identity transparency | Real name, bio | Not available |
| Published work | Recognized platforms | Not found |
| Citations | Referenced by others | None |
| Authority signals | Backlinks, mentions | Absent |
| Trust indicators | Contact/editorial info | Missing |
Verification Takeaway
If an author fails 3 or more E-E-A-T checks, treat the content as low-trust.
Author decached heladim jomsel fails all major checks, indicating high verification risk.
SEO and Semantic Implications of Unknown Author Entities
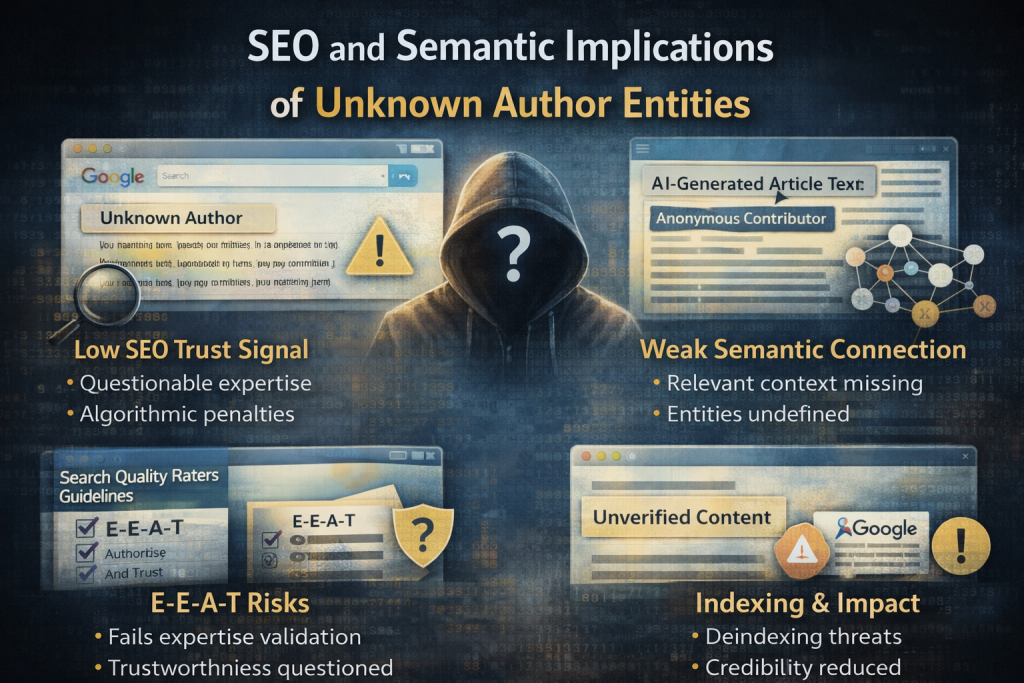
Impact on Content Credibility
Using names like author decached heladim jomsel can:
- Reduce perceived trustworthiness
- Lower ranking potential
- Trigger quality evaluation flags
(According to Google quality evaluation principles…)
Knowledge Graph Limitations
Search engines rely on entity recognition:
- Verified authors → included in knowledge graphs
- Unknown entities → ignored or weakly indexed
Author decached heladim jomsel falls into:
- Non-recognized entity category
Risks of Citing Unverified Authors
Citing author decached heladim jomsel may lead to:
- Misinformation propagation
- Reduced content authority
- Poor SEO performance
Table: Verified vs Unverified Entity in SEO
| Factor | Verified Entity | Unverified Entity |
|---|---|---|
| Ranking potential | High | Low |
| Trust signals | Strong | Weak |
| Citation value | Reliable | Risky |
| Knowledge graph inclusion | Yes | No |
Takeaway
For strong SEO performance, always prioritize verified entities over unknown names like author decached heladim jomsel. This aligns with E-E-A-T and improves ranking stability.
Should You Trust Content from Unknown or Unverified Authors?
Risk Assessment
Content published under unverified or ambiguous author identities carries measurable risks in both informational accuracy and SEO performance. These risks include:
- Lack of accountability: No identifiable individual or organization responsible for the content
- Increased misinformation probability: Content may not be fact-checked or peer-reviewed
- Low editorial standards: Often associated with automated or bulk publishing systems
- Unclear expertise level: No credentials or subject-matter authority
From a search quality perspective, such content is often classified as low-trust due to missing E-E-A-T signals (Experience, Expertise, Authority, Trust).
When It May Be Conditionally Acceptable
There are limited scenarios where content from unknown authors may still provide value:
- Technical documentation or code snippets that can be independently verified
- User-generated insights on forums where multiple contributors validate information
- Non-critical topics where accuracy has minimal real-world impact
However, even in these cases, verification through cross-referencing is essential.
When to Avoid Completely
Avoid relying on such content in the following contexts:
- Medical, financial, or legal information
- Academic research or citations
- Professional decision-making
- SEO content intended for ranking
These areas require high-authority, verifiable sources to maintain credibility and accuracy.
Pros vs Cons Table
| Pros | Cons |
|---|---|
| May provide unique or early insights | Low credibility and trustworthiness |
| Sometimes useful in niche or experimental topics | No verifiable expertise |
| Can reflect emerging or anonymous perspectives | High risk of misinformation |
| Accessible across multiple platforms | Not recognized by search engines |
Summary
Unverified authors may occasionally provide useful insights, but they lack essential trust signals. For high-stakes or SEO-driven content, they should not be used as primary sources.
Common Reasons Unknown Author Names Appear Online
AI Content Generation Systems
Automated content generation tools frequently assign default or synthetic author names when:
- No author field is specified
- Bulk content is generated programmatically
- Metadata is incomplete or auto-filled
This results in structured but non-human identities appearing across multiple pages.
Data Scraping and Aggregation
Content aggregation systems often pull data from various sources without preserving original attribution. This can lead to:
- Broken or altered author names
- Misattributed content
- Creation of entirely new identity labels
Experimental SEO and Testing Environments
SEO professionals and developers use placeholder identities to:
- Test indexing behavior
- Analyze crawl patterns
- Evaluate ranking signals
These names are not intended for public authority but may still become indexed.
Anonymous and Pseudonymous Publishing Trends
Some authors intentionally publish without revealing their real identity. Reasons include:
- Privacy protection
- Avoiding bias or scrutiny
- Publishing controversial or experimental ideas
While anonymity is not inherently negative, it reduces trust unless supported by consistent, high-quality output.
Summary
Unknown author names typically originate from automation, testing, or anonymity. Their presence does not indicate credibility and should always trigger verification.
Practical Steps to Evaluate Content Credibility
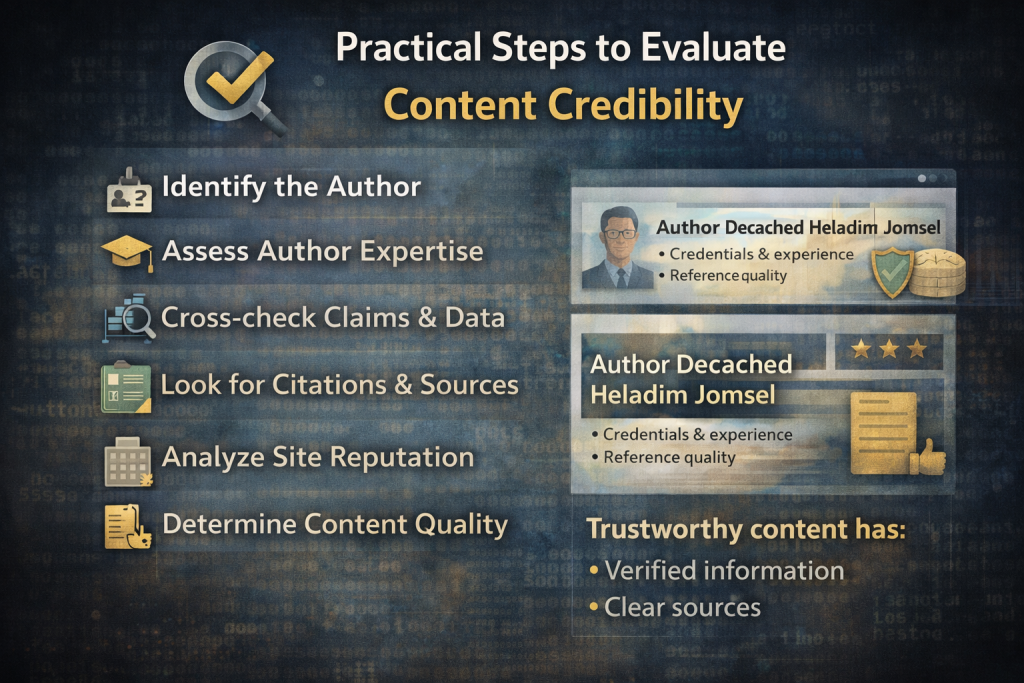
Cross-Verification
Always compare the information with:
- Established industry sources
- Official documentation
- Recognized experts or institutions
If multiple trusted sources confirm the same information, reliability increases.
Content Quality Analysis
Evaluate the content itself:
- Is the information structured and logically consistent?
- Are claims supported with data or examples?
- Does it follow industry standards?
Low-quality or vague content is a strong indicator of unreliability.
Source Transparency
Check for:
- Author biography or credentials
- Publisher information
- Editorial guidelines
Lack of transparency directly impacts trustworthiness.
External Validation Signals
Look for:
- Backlinks from reputable websites
- Mentions in authoritative publications
- Citations in credible sources
Absence of these signals suggests low authority.
Table: Content Credibility Evaluation Framework
| Evaluation Factor | High-Quality Content | Low-Quality Content |
|---|---|---|
| Source transparency | Clear author and publisher | Missing or vague identity |
| Supporting data | Evidence-based | Unsupported claims |
| External validation | Strong backlinks and citations | No references |
| Consistency | Logical and structured | Inconsistent or unclear |
Summary
Credibility is determined by verifiable signals, not just content presence. Always validate before using or citing any information.
SEO Implications of Using Unverified Sources
Impact on Rankings
Search engines prioritize content that demonstrates:
- Clear authorship
- Authority and expertise
- Trustworthy sourcing
Using unverified sources can:
- Reduce page quality scores
- Lower ranking potential
- Increase risk of devaluation
E-E-A-T Alignment
E-E-A-T is a core evaluation framework in modern SEO:
- Experience: First-hand knowledge
- Expertise: Subject-matter understanding
- Authority: Recognition by others
- Trust: Transparency and reliability
Unverified authors typically fail across all four dimensions.
Content Quality Signals
Search engines analyze:
- Author reputation
- Content depth and accuracy
- Source credibility
Weak signals in these areas negatively impact indexing and ranking.
Table: SEO Impact Comparison
| SEO Factor | Verified Sources | Unverified Sources |
|---|---|---|
| Ranking stability | High | Low |
| Trust signals | Strong | Weak |
| Indexing priority | High | Low |
| User engagement | Higher | Lower |
Summary
From an SEO perspective, relying on verified and authoritative sources is essential for sustainable rankings and credibility.
Conclusion
Unverified author identities represent a growing pattern in modern digital publishing, largely driven by automation, anonymity, and experimental content systems. While they may occasionally provide useful insights, they lack the foundational signals required for trust, authority, and reliability.
For both users and content creators, the best practice is to prioritize verifiable, transparent, and authoritative sources. This approach aligns with search engine quality standards and ensures accurate, dependable information.
Frequently Asked Questions
1. How can I check if an author is legitimate?
Verify the author’s identity through:
- Published work on trusted platforms
- Professional profiles
- Citations and backlinks
Lack of these signals indicates low credibility.
2. Are anonymous authors always unreliable?
No, but they require additional verification. Anonymous content can be credible if:
- It is consistent
- Supported by evidence
- Verified through external sources
3. Why do strange or unknown author names appear online?
They typically result from:
- AI-generated content
- Data scraping systems
- Testing or placeholder environments
4. Can AI generate fake author identities?
Yes. AI systems can create realistic but non-existent names when:
- Generating content at scale
- Filling missing metadata fields
5. Is it safe to cite unknown authors in SEO content?
No. Citing unverified authors can:
- Reduce credibility
- Harm SEO performance
- Increase misinformation risk
6. What is the safest way to use uncertain information?
Cross-check it with:
- Official sources
- Recognized experts
- Industry-standard documentation
7. Do search engines recognize all author names?
No. Search engines prioritize entities with:
- Established authority
- Consistent identity
- Verified presence
Unknown entities are often ignored or weakly indexed.
References
- Google Developers
https://developers.google.com/search/docs/fundamentals/creating-helpful-content - Google Search Quality Evaluator Guidelines
https://static.googleusercontent.com/media/guidelines.raterhub.com/en//searchqualityevaluatorguidelines.pdf - Ahrefs
https://ahrefs.com/blog/eat-seo/ - Search Engine Journal
https://www.searchenginejournal.com/google-eat/quality-raters-guidelines/ - Search Engine Journal
https://www.searchenginejournal.com/your-guide-to-google-e-a-t-seo-ebook/413099/ - Moz
https://moz.rankious.com/_moz/learn/seo/google-eat